Checkpoint Endpoint Security Logo

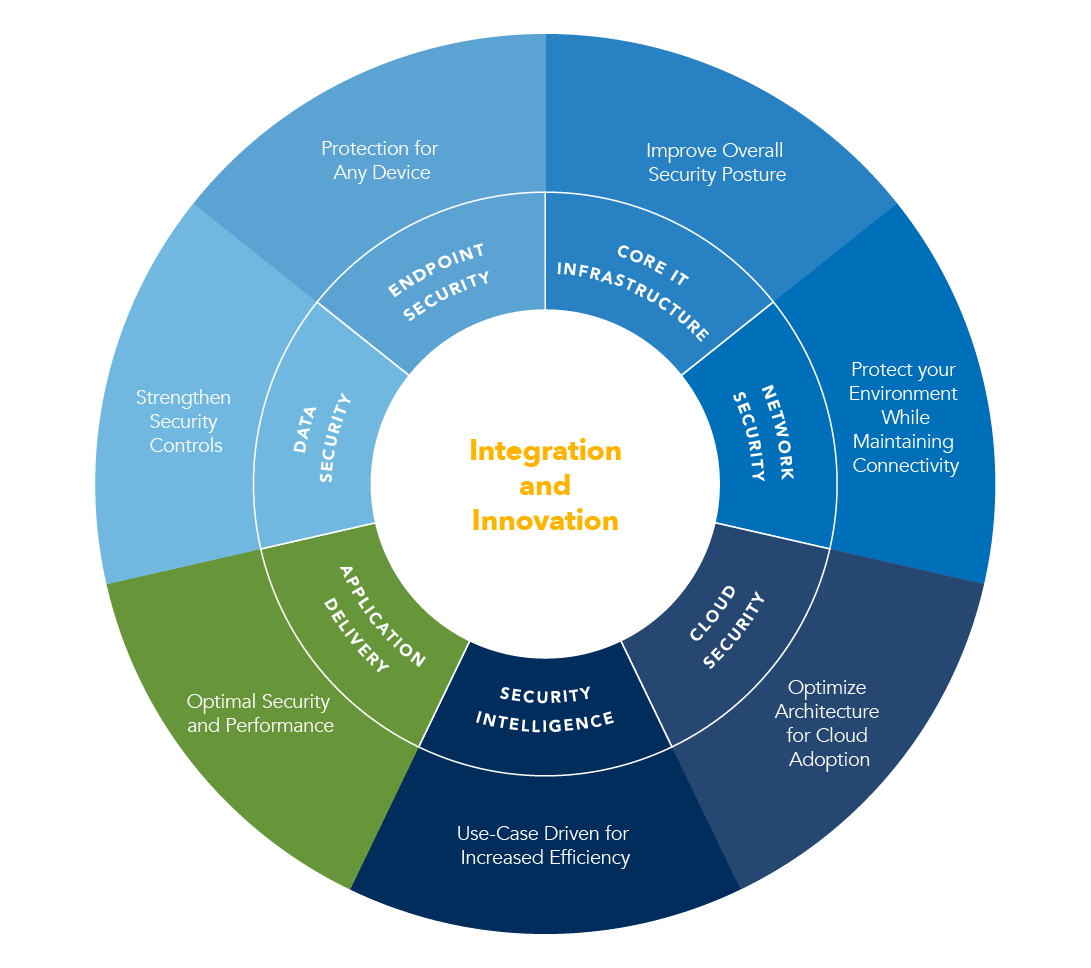
Today s borderless networks are redefining endpoint protection.
Checkpoint endpoint security logo. Check point infinity architecture. As an integrated suite endpoint security provides simple unified management and policy enforcement. Copyright privacy policy privacy policy. The only fully consolidated cyber security architecture that provides unprecedented protection against gen v mega cyberattacks as well as future cyber threats across all networks endpoint cloud and mobile.
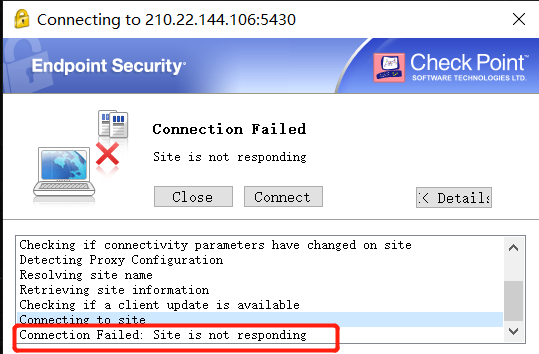
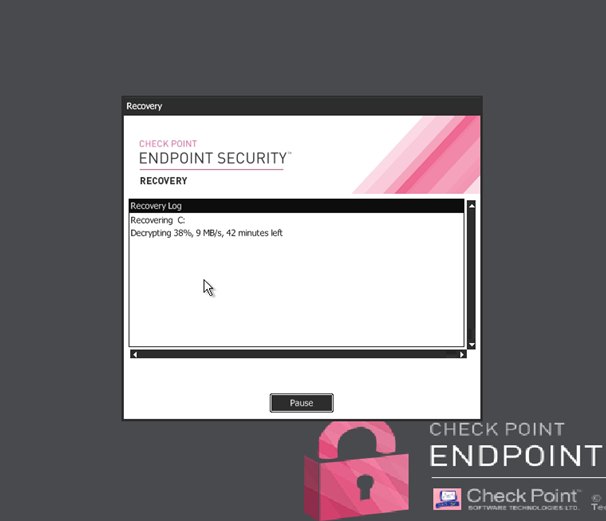
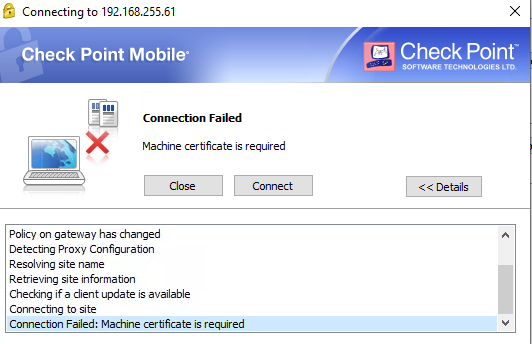
Upon being installed the software adds a windows service which is designed to run continuously in the background. Split dns uses a securemote dns server an object that represents an internal dns server that you can configure to resolve internal names with private ip addresses rfc 1918. 1994 check point software technologies ltd all rights reserved. During setup the program creates a startup registration point in windows in order to automatically start when any user boots the pc.
Makes no representation or warranties either express or implied by or with respect to anything in this document and shall not be liable for any implied warranties of merchantability or fitness for a particular purpose or for any indirect special or consequential damages. Check point endpoint security is a software program developed by check point inc. With a variety of endpoints freely accessing networks they re storing sensitive corporate data. I was flabbergasted when both responses was along the lines of hmmm i ve never sent that before so and so works fine after months of digging around the internet and trying various things like re installing removing other apps and doing a fresh os install with a.
Because 70 percent of successful data breaches start on endpoints 1 a preventative approach to endpoint security can help stop cyber attacks. Check point software technologies ltd. Sandblast agent is the advanced. It is best to encrypt the dns.
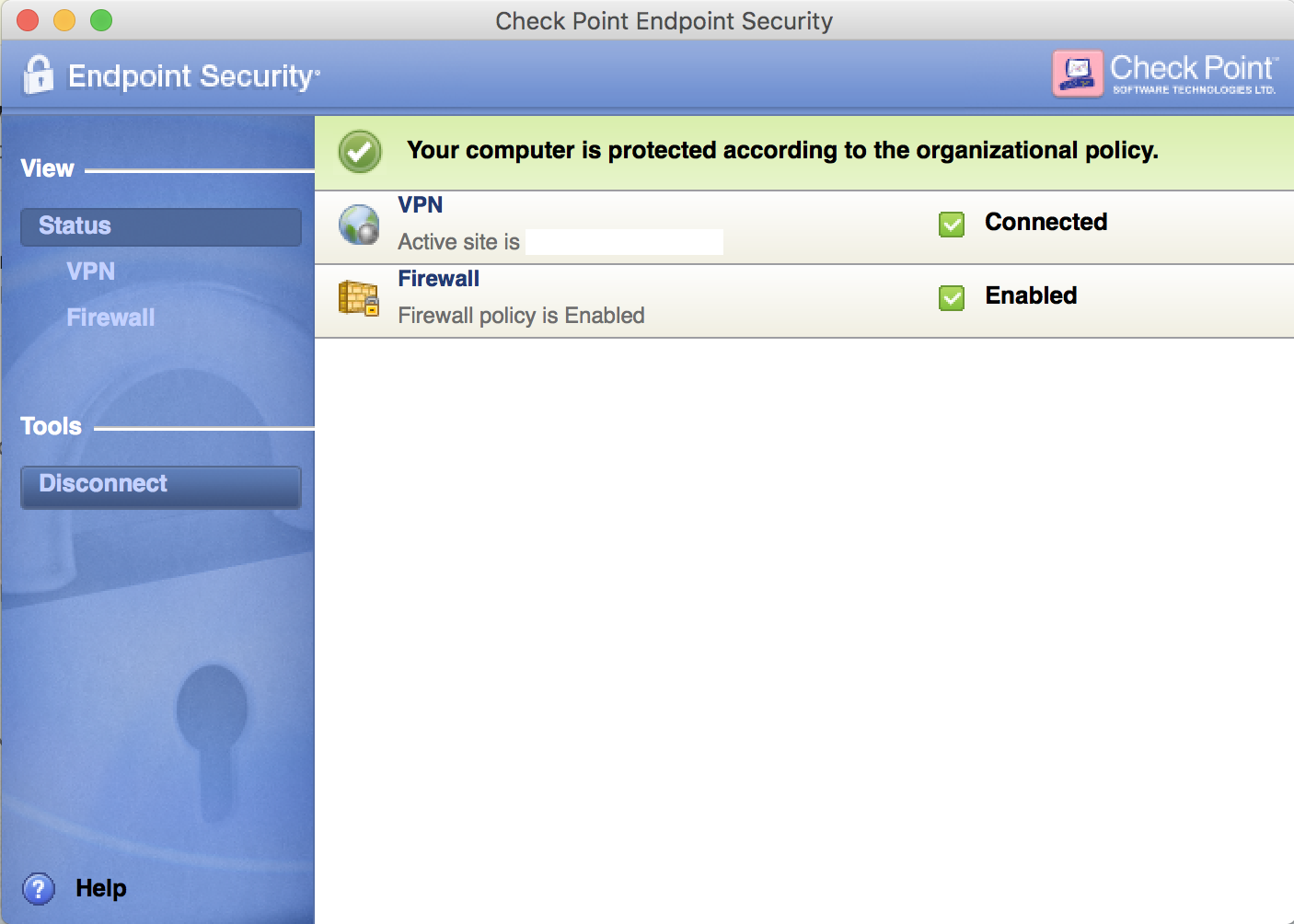
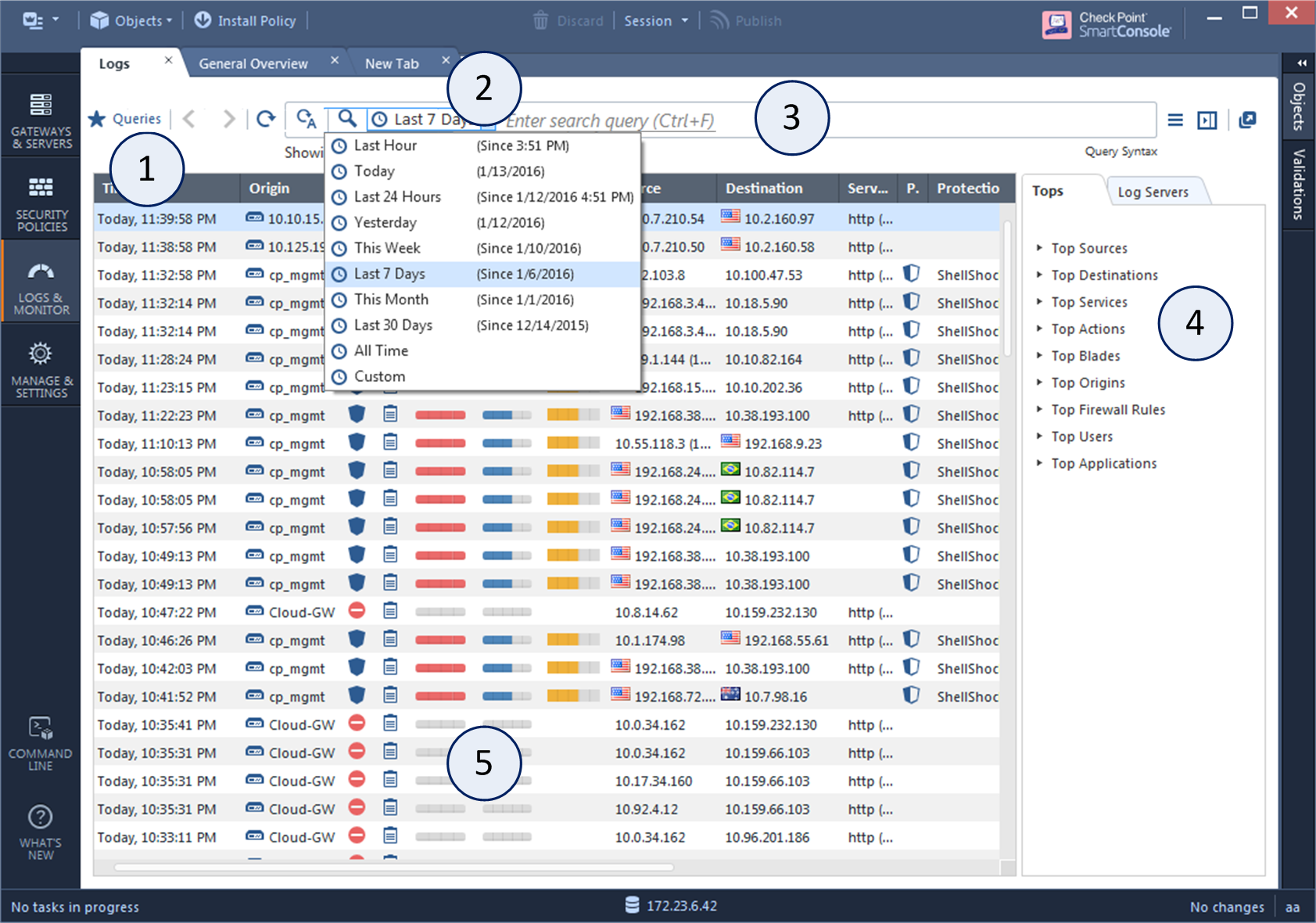
Check point endpoint security includes data security network security advanced threat prevention forensics endpoint detection and response edr and remote access vpn solutions. I had talked to a mac specialist and a checkpoint security specialist. We advise customers who use bitlocker to install enterprise endpoint security e83 00 or higher due to significant limitations in. Check point endpoint security is a single agent providing data security network security threat prevention and a remote access vpn for complete windows and mac os x security.
For securemote use the split dns feature. For endpoint security vpn and check point mobile for windows use office mode.